According to a recent report, in 2022, 82% of all data breaches involved ‘the human element’ (the use of stolen credentials, phishing, misuse or human error).
This statistic is a stark reminder of the importance of email security in today’s digital landscape, particularly for Australian businesses.
With email being one of the primary communication channels used by businesses across all industries, it’s not surprising that cybercriminals are increasingly targeting email accounts in their attempts to gain unauthorised access to sensitive data or networks.
By understanding the nature of these security threats and taking proactive steps to address them, businesses can safeguard their data and ensure the continued trust of their clients and partners.
Get more insights like these
Receive advice from our industry-leading cyber security experts.
Tekspace will never send you spam or share your email address with a third-party.
Email Security Threats
1. Phishing
Phishing is one of the most common email security threats faced by businesses today.
In fact, the global average cost of a successful phishing attack was $4.91M USD (approx. $7.1M AUD) in 2022.
Phishing attacks typically involve an attacker sending an email that appears to be from a legitimate source, such as a bank or other trusted organisation, in an attempt to trick the recipient into providing sensitive information such as login credentials or financial data.
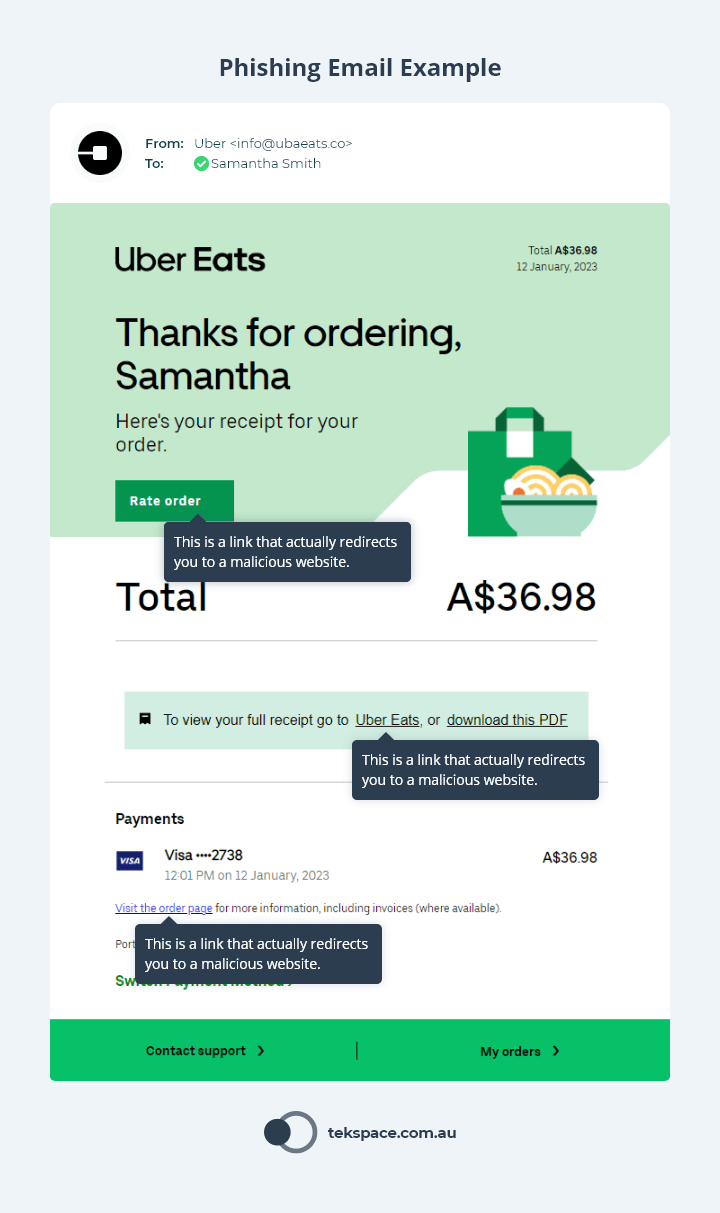
In recent years, phishing attacks have become increasingly sophisticated and difficult to detect.
Attackers use social engineering techniques to create a sense of urgency or fear in the recipient, encouraging them to take immediate action without thinking things through.
They may also use well-crafted emails that closely mimic the language and branding of a legitimate organisation, making it difficult for even the most discerning users to spot the fake. The release of AI apps (LLMs) like ChatGPT have also assisted bad actors in producing far more convincing and sophisticated phishing emails.
2. Spear Phishing
Spear phishing is a significant email security risk that can have serious consequences for businesses.
Unlike traditional phishing attacks, which are sent to a large number of recipients in the hope that a few will take the bait, spear phishing attacks are highly targeted and personalised.
Attackers use information gleaned from social media and other online sources to create convincing emails that appear to come from a trusted source.
This personalisation makes spear phishing attacks such an effective email security threat. For example, an attacker may send a spear phishing email to an employee in the finance department, pretending to be the CEO and requesting a wire transfer.
One rather insidious type of spear phishing attack is Business Email Compromise (BEC).
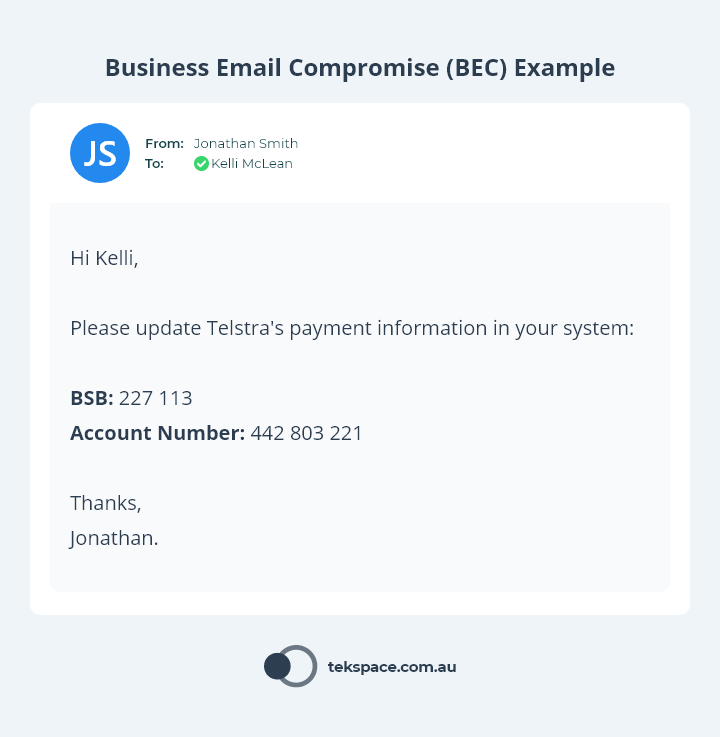
In a BEC attack, an attacker gains access to a legitimate email account and uses it to deceive employees, customers, or vendors into transferring money or sensitive information. The attacker may use a legitimate email account, and the email may appear to be a normal business transaction.
In 2022, the median transaction size resulting from BEC attacks was $60,000 USD (approx. $87,000 AUD).
Additionally, BEC attacks can occur over a long period of time, with the attacker slowly building trust and gathering information over several weeks or months.
BEC attacks can have significant financial and reputational consequences for businesses.
3. Man-in-the-Middle Attacks
Man-in-the-middle (MitM) attacks are a sophisticated email security threat that can result in data theft, financial loss, and reputational damage for businesses.
In a MitM attack, an attacker intercepts the communication between the sender and recipient. The attacker can then eavesdrop, modify the contents of the email, redirect it to a different recipient, or even delete it entirely.
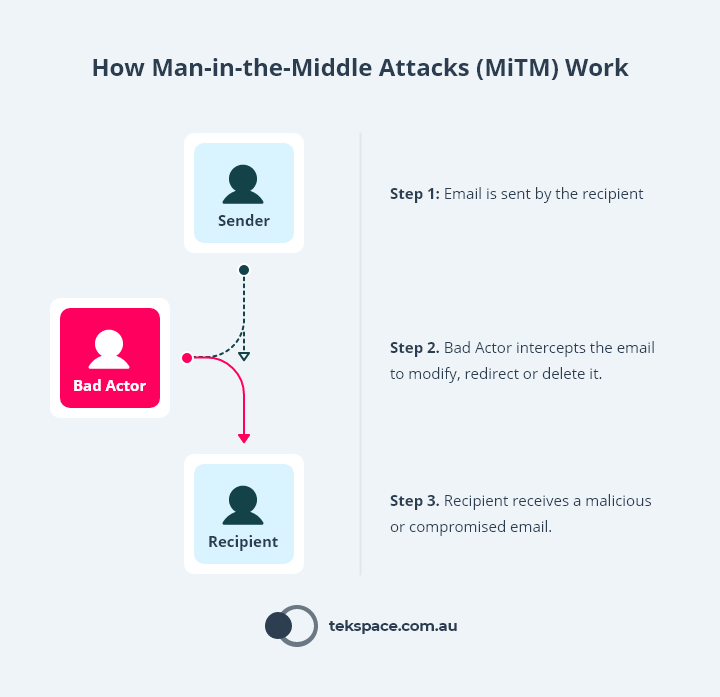
To execute a MitM attack, an attacker might compromise a Wi-Fi network, exploit vulnerabilities in the email server, or using a phishing attack to gain access to an email account.
MitM attacks are email security threats that can be difficult to detect, as they can occur without the knowledge of either party involved in the communication.
However, there are some warning signs that may indicate a MitM attack is taking place, such as unexpected changes in email behaviour or the presence of unfamiliar IP addresses in email headers.
4. Email Hijacking
Email hijacking is a serious email security threat that occurs when an attacker gains unauthorised access to an email account.
This can happen through a variety of means, such as social engineering, password cracking, or malware.
Once an email account is hijacked, the attacker has access to all of the information stored within it, including sensitive business data, personal information, and confidential communications.
The attacker can also use the hijacked account to send spam or malicious emails, further compromising the security of the account and potentially damaging the reputation of the business.
One of the challenges of email hijacking is that it can be difficult to detect. The attacker may use the account for some time without the knowledge of the owner, and may only be discovered when the owner notices unusual activity or is alerted by another party.
How to protect against email security threats
While these email security threats can cause significant harm to businesses, there are a variety of solutions available to address cyber security risks.
Next Generation API Email Security, Security Awareness Training, and Data Loss Prevention (DLP) are just a few of the tools that can help protect against phishing, spear phishing, man-in-the-middle attacks, business email compromise, and email hijacking.
Let’s explore these solutions in more detail and how they can help reduce your email security risk.
Next Generation API Email Security
Next Generation API Email Security is a powerful weapon for combating email security threats.
Today, between 31.5% and 68.6% of businesses use Microsoft 365 and Google Workspace as their email service provider.
And while both of these services have their own built-in email security capabilities, malicious emails still get through the cracks.
In fact, an analysis of more than 300 million emails from Check Point shows that for every 100k emails, Microsoft and Google still miss and deliver 626 and 932 malicious emails respectively.
Why? Well, the popularity of these platforms makes them a target, and the traditional use of Secure Email Gateways (SEGs) doesn’t cut it anymore.
Just like Google and Microsoft, API Email Security solutions live in the cloud too.
But unlike traditional SEGs, email flows through Microsoft or Google first, then the API Email Security solution and on to the user.
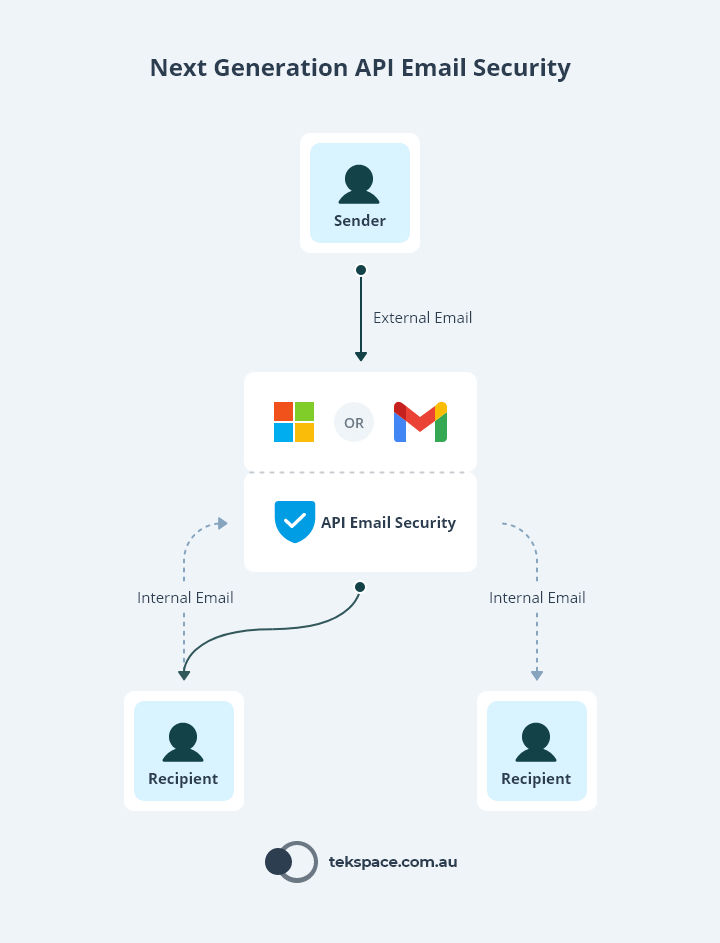
This means that you get all the benefits of Microsoft or Google’s email security protections, plus you never reveal who your API Email Security vendor is, and you can scan emails as they move between staff and systems.
API Email Security really is the best way to protect staff from email security threats.
Data Loss Prevention (DLP)
Data Loss Prevention (DLP) is a cyber security measure that is designed to prevent sensitive data from unauthorised access and loss.
DLP solutions give you the ability to define the types of data that your organisation deems as ‘sensitive’, then set actions that the DLP software should follow if it detects a breach.
In the context of email security threats, DLP tools can be used to:
- Block the transmission of sensitive data, such as personally identifiable information, financial information (such as credit card numbers) and medical records.
- Automatically encrypt sensitive data if it leaves the organisation.
- Generate real-time alerts to key stakeholders when DLP policies are breached.
- Comply with regulatory requirements by monitoring email traffic for sensitive data and generating reports on data usage. This can help organisations demonstrate compliance with regulations such as HIPAA, GDPR, or PCI-DSS.
Security Awareness Training
While Next Generation API Email Security and Data Loss Prevention (DLP) solutions are crucial in protecting against email security threats, it’s important not to forget about the human element.
Employees can be an organisation’s weakest link, so ensuring they are educated and aware of email security threats is critical. Security Awareness Training (SAT) is an effective way to train employees and improve their knowledge of email security threats.
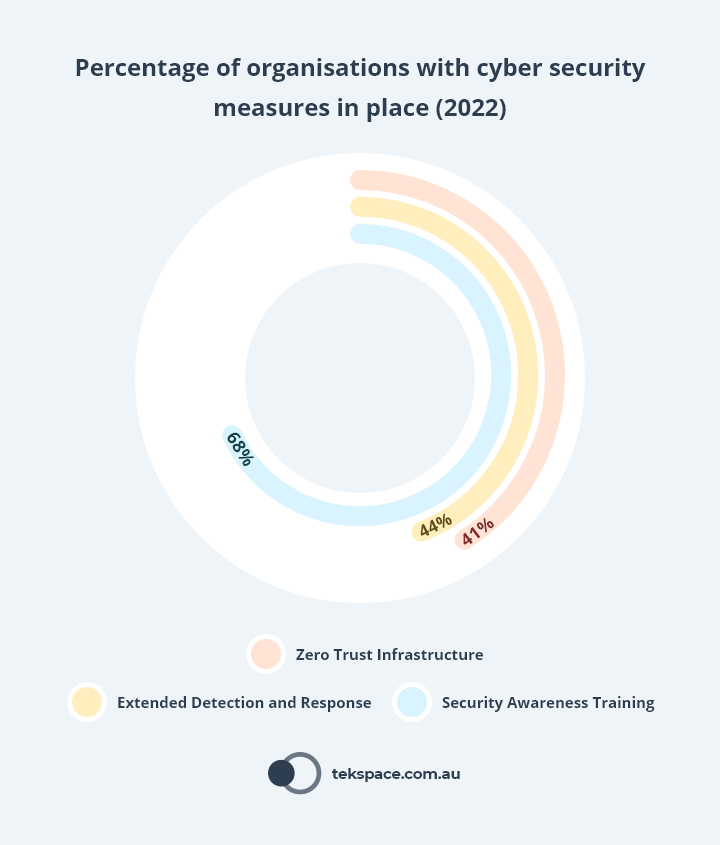
In 2022, the Australian Government reported that 68% of organisations had Security Awareness Training in place.
This sounds like a lot, but in reality, most of these organisations were only delivering training once annually.
Modern SAT solutions can operate autonomously and continuously, with little human management or overhead and can dramatically improve staff education.
Gone are the days of one-off training sessions that everyone forgets. Deploying these solutions is also quick, taking under an hour.
They can also identify individual staff’s knowledge gaps and send them phishing simulations to address these gaps. This means that no two staff receive the same simulation at the same time, improving the likelihood that everyone is learning what they need to know.
Deploying these solutions is also quick, taking under an hour.
By investing in SAT solutions, organisations can better protect themselves against email security threats and minimise the risk of security breaches. To learn more about SAT, check out our Definitive Guide to Security Awareness Training in 2023.
Conclusion
In conclusion, email security threats are a very real danger to Australian businesses in 2023.
The top 4 threats outlined in this article are just the tip of the iceberg, and it is imperative that businesses take steps to protect themselves from these threats.
The solutions outlined in this article, including Next Generation API Email Security, Data Loss Prevention (DLP), and Security Awareness Training, are just a few of the many measures that businesses can take to protect themselves.
By taking these steps and remaining vigilant against email security threats, Australian businesses can ensure that their data and operations remain safe and secure.
Get more insights like these
Receive advice from our industry-leading cyber security experts.
Tekspace will never send you spam or share your email address with a third-party.